(Not THAT one, the OTHER one!)

Though I started my career in software development writing embedded software for Aerospace Avionics Systems, I’ve spent the past 3 years working in the Supply Chain space, starting just before COVID-19 hit the world.
I had worked the past 20 years in the eCommerce space, mainly in retail/CPG, working to help design, build, analyze, and optimize revenue (and promotions!) for my clients selling their products via web and mobile. In 2020, I decided to dig in to the one area of eCommerce and selling goods to consumers that I had not delved into but was looking like it was going to be a huge problem area due to disruptions caused by a global pandemic: The Supply Chain. Transportation & Logistics. Inventory Management.
I worked with many shippers and freight forwarders as they turned 5-year plans into 3-month plans. Projects popped up and were funded. Curb-side pick-up. BOPIS (Buy On-Line Pick up in store), BORIS (Buy On-Line Return In-Store). Retail clerks and cashiers were now being trained in warehouse processes, such as “pick-and-pack”, and IT systems were developed and accelerated overnight, it seemed, to support these new processes.
The biggest lesson learned? It wasn’t technology. It was people. People adapting and learning new processes that literally were being designed, implemented, supported by shiny new technology and updated systems, and rolled out as fast as possible.
Now let’s look at a different kind of supply chain that hasn’t been around as long but is probably more key and more misunderstood than any single area in technology that I’ve seen in my entire career.
The Software Supply Chain.
It’s not Rocket Science, but it’s close
As I mentioned earlier, I started my career in Aerospace writing software for airplanes. I was put in charge of ensuring that the software we wrote for the Lockheed Martin C-130J, the first fly-by-software airplane developed by Lockheed Martin, was certifiable by the FAA. Simple, right? No. (You can read about it Here .)
The software had to be more than 99.999% solid. Failures were measured in potential lives lost. (How’s that for your KPI?)
So, what did we learn? We learned that there were certain processes that we were rock solid in as a company and an industry. Requirements definition, systems design, architecture, unit, and component testing, etc. (Solid silos!)
What were we not so good at? Any process that spanned a responsibility domain. Like systems integration testing. (Two systems, or dozens of systems, having to work together.). Separate teams were good at what they knew how to do, and not good at focusing upstream or downstream on the conveyor belt.
We set out to solve the problem. Enter ISO-12207. The US Commercial Software Standard.
First, You Build the process framework.
The two main contractors of the time, Lockheed Martin and Boeing, decided to lay the groundwork to fix the problem going forward, while laying down best practices for future programs.
So, we built a process framework. (Yes, “we”. I was on the team and owned the Lockheed Martin piece.) What’s a process framework? It’s the “what” of the software/systems development process. It tells you what processes to have, and where they fit. (Not the “how”. The “how” would be details that would use this framework, such as “Agile”, “Waterfall”, etc.)
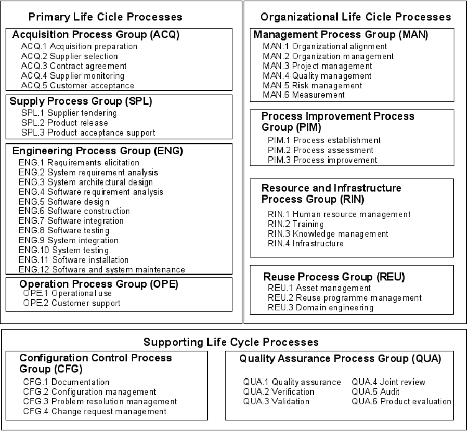
Figure 1 – ISO 12207 Lifecycle Process Standard
(Credit to ResearchGate .)
When we wrote this process, we felt the key areas were what we called the “Supporting Processes”. These processes are the foundation that forms the basis for what I call the “Software Conveyor Belt”.
The software conveyor belt travels from left to right. It starts on the left. (Important for later.) An idea, a business requirement, leading to design, code, unit test, then handoff to QA, tested, then continuing onto production for everyday use.
So, what’s the problem?
The problem is actually very simple to identify. (Not so simple to fix.)
The weaknesses in complicated systems/software development, whether it’s aircraft avionics software, eCommerce mobile and web applications software, or any other type of software, such as Cloud-Based software, are always the same.
Supporting processes that span organizations, or domains (e.g. development team, QA team, operations team), are ALWAYS problem areas. Why? People skill sets do not span domains. Companies historically don’t hire that way, and software vendors do not build tool environments that way, nor do they have the skill sets to sell that way, anyway. (And colleges certainly don’t educate that way, but that’s a whole other blog topic.)
And the problems are always are in these areas: Non-Functional Requirements and what I’ve always called, “The Big 3”. Configuration, Change and Release Management. That is the foundation of your conveyor belt—and it has to be rock solid.
Non-Functional requirements include the following:
- Performance Testing
- Security
- Usability
- Availability, Reliability, Maintainability & SLAs
- Certification & Compliance (Including PII, GDPR, etc.)
- Portability, Compatibility & Localization
- Functionality & Extensibility
Non-functional requirements span organizational domains, expertise areas and in many cases, haven’t been, or aren’t, part of someone’s performance KPI. (In other words, no one owns them across the organization, so they aren’t implemented correctly and do not become a focus unless an event occurs to make them a focus. Think Black Friday website crash or data breach/malware intrusion putting your company on the front page of the Wall Street Journal.)
How to fix the problem, or at least where to start
First, ditch the acronyms. Now. Just stop. They started with some marketing team for a SaaS vendor trying to do something catchy for their shiny new point product being sold with no process in mind.
Let’s start with this one: Shift Left. Stop using it. If you have to shift left, then you didn’t do it right from the start in the first place.
Say what? Remember what I said earlier. The conveyor belt for the software supply chain starts on the left. If you aren’t doing that already, with one or all the non-functional requirements I list above, or the “Big 3”, drop everything and do that. Or hire someone to show you how to do that. (Shameless plug here, my email is below. I do this in my sleep.)
The biggest problem areas that cause the Wall Street Journal front page articles are typically performance testing and security these days., though I’d argue that compliance is right up there as well. (Think GDPR and PII.)
The next ones to dump: DevOps & DevSecOps.
Why? For the same reasons as shift left, but also because many vendor offerings I see have “test” dumped inside development, or have placed “reliability” in Operations. (Or one I hear often, “We go from “Dev to the Cloud!” Say what? The cloud is not a process. You might want to dig deeper to explain what you mean there. But I digress.)
Other than not knowing the process, or that marketing who never wrote a line of code in their life, had nowhere else to put it, it’s fine. (Not!). I won’t shame any SaaS company, but there’s not one application performance or cloud security company that presents this accurately. (Go ahead, prove me wrong. I’ll wait.)
So what now? Where should you start?
Enter the Software Supply Chain & Software Bill of Materials (SBOM)
Going back to my introduction around the certification of software for the FAA with DO-178C, we introduced something new: Software Bill of Materials (SBOM). The FAA had long had a Hardware Bill of Materials, but software in an airplane was very new for us. So we decided to lift the hardware BOM and utilize the framework and best practices hardware had for our use in software. (It had no “H” in front of it back then. No need to.)
What does this mean today?
An SBOM is a complete list of all software used in the development, testing and execution/production of an application. This includes all tooling (including cloud components, and the bits and pieces that tooling brings to the table), as well as any data, embedded software/website url’s, links, pixels, tags, open source libraries, etc.
And typically, this SBOM can literally change on the fly, without any notification, if the right safeguards are not in place for things like application monitoring, security/vulnerability scanning, etc. (In other words, the ”supporting processes” I discussed earlier.)
Here’s an example of part of a stack from an online retailer’s website. This is a cross-section example of what gets stuck on a conveyor belt:

Example 1 – Output from Webpage Test by Catchpoint.
So what’s the problem, you say?
Each one of these components listed is provided by a third party and is part of your SBOM. And it can change on the fly, and typically does particularly for web and mobile based applications, and cloud-based applications.
See the problem? Without sound processes in place, especially around the key ones I listed above, you are vulnerable. You are vulnerable wherever you have gaps.
What’s an example of a gap? One example would be inclusion of a third party pixel or tag on your website that gets changed or modified without your knowledge. How would that ever happen? Easy. Poor configuration, change and release management. Poorly integrated tools to manage that process. Point products over platform. (But just because a vendor says they have a platform, doesn’t necessarily mean its components are integrated against some standard. (Many are not.)
And “integration” is very much a misunderstood and over-used term. Did you know that there are 7 layers of integration? There are. The model is here: OSI Model. (Digging into what this means would be another blog, but I wanted to bring it up anyway.)
How about another example? How about security vulnerabilities? With a lot of today’s application development also occurring in the cloud, security must certainly start from the left, at the commencement of the systems/software development lifecycle. It must include development environments, containers, infrastructure as code, etc.
Many of the current SaaS vendors in the cybersecurity and performance space reference directives such as Executive Order 14028, the NIST minimum standard for testing in order to promote their compliance and why they should be your vendor of choice.
What don’t they mention? That the Executive Order also specifically references ISO 12207 as the process framework to use for your conveyor belt. (As does its follow-on guidance, NISTIR 8397. Section 1.1) And why wouldn’t they mention it? It’s most likely due to a lack of understanding that a software conveyor belt, and for that matter, an SBOM, really has at its underlying foundation, a software process framework. You can’t sell what you don’t understand. (Too bad, too, because that’s where the value and benefit lies the most.)
So what should you look for and what should you do?
Call to Action
Figure out what you want your conveyor belt to look like and where the gaps are. Pick one key focus area and start there. Is it performance/usability? Is it security? Only then should you start filling in the technology gaps. (And by gaps, the most important ones are the ones I mention above that span silos.)
Are you looking at vendors who claim to “have a platform”? Ask the tough questions. Lay their “platform” against the process framework and conveyor belt. Does it still hold water? Where are the gaps?
I’ve seen a lot of “platforms” come and go over the years, whether they were software development “Integrated Development Environments” that didn’t even integrate their own tools together, or “Business Technology Optimization (BTO)”, where the former Mercury Interactive first started nobly integrating QA/test and production, to today’s shiny new “Cloud-Native Application Protection Platforms (CNAPP)”. They all had/have one thing in common: No process foundation for the conveyor belt. And no focus to help their customers get one via a mature professional services offering.
Start with asking your vendors for their SBOM for their solution. You’d be amazed at the amount of open source and third party software that they use and bundle into their solution. (It’s usually found in their SaaS agreement.)
So, assess your “as-is” first. Your gap is your implementation project plan and the “to-be” as well as your roadmap. Lay your technology down against the process. Keep what fits, ditch what doesn’t. Then fill in the gaps based on criticality. Is GDPR and PII a concern? Start there. How about cloud application vulnerability? Usability and performance?
Any of those can get you company on the front page of the Wall Street Journal, and not in a good way. Better start now.
And leave the acronyms at the door.
Questions? My e-mail is dan@CAVU-Global.io